IPSec_×××之H3C
发布时间:2019-09-14 09:27:22编辑:auto阅读(2294)
一、部署IPsec关键点:
1) 先定义 ACL 和保证需要加密的数据 IP层可达;
2) 要定义 IKE Proposal、IKE Peer、IPSec Proposal 和 IPSec Policy;
3) 注意上述配置中只有 IPSec Policy 配置需引用 IPSec Proposal 和 IKE Peer;
4) 将定义好的 IPSec Policy 绑定到指定的出接口。
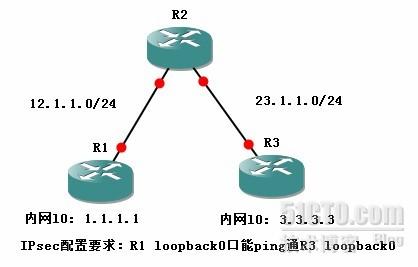
二、实验Toplogy
三、实验步骤:
1、省略R1、R2、R3的接口IP配置
2、R1:
1.配置需要加密传送的ACL
[R1]acl num 3000
[R1-acl-adv-3000]rule permit ip source
2.IKE策略配置
[R1]ike proposal 10 //创建IKE提议,并进入IKE视图
[R1-ike-proposal-10]encryption-algorithm 3des-cbc //使用3DES的加密算法
[R1-ike-proposal-10]authentication-method pre-share //使用预设口令身份验证方式
[R1-ike-proposal-10]authentication-algorithm md5 //使用md5的认证算法
[R1-ike-proposal-10]dh group2 //使用的DH交换组
[R1-ike-proposal-10]sa duration 86400 //ISAKMP SA生存周期
[R1-ike-proposal-10]q
3.配置IKE对等体及密钥
[R1]ike peer R3 //创建IKE对等体,并进入IKE对等体视图
[R1-ike-peer-r3]exchange-mode main //IKE对等体的协商模式
[R1-ike-peer-r3]pre-shared-key h
[R1-ike-peer-r3]local-address
[R1-ike-peer-r3]remote-address
[R1-ike-peer-r3]remote-name R3 //对等体安全网关名称
[R1]ike local-name R1 //本端安全网关名称
4. IPSEC安全提议配置
[R1]ipsec proposal r1 //创建IPSEC安全提议
[R1-ipsec-proposal-r1]transform esp //安全协议
[R1-ipsec-proposal-r1]esp encryption-algorithm 3des //ESP协议采用加密算法
[R1-ipsec-proposal-r1]esp authentication-algorithm md5 //ESP协议采用认证算法
[R1-ipsec-proposal-r1]encapsulation-mode tunnel //ESP协议采用工作模式
[R1-ipsec-proposal-r1]q
5.配置IKE协商的安全策略
[R1]ipsec policy 1 10 isakmp //创建一条安全策略
[R1-ipsec-policy-isakmp-1-10]security acl 3000 //配置加密传送所需的ACL
[R1-ipsec-policy-isakmp-1-10]proposal r1 //配安全策略所引用的安全提议
[R1-ipsec-policy-isakmp-1-10]ike-peer r3 //引用的IKE对等体
[R1-ipsec-policy-isakmp-1-10]pfs dh-group2 //DH组
[R1-ipsec-policy-isakmp-1-10]sa duration time-based 86400 //ipsec SA生存周期
[R1-ipsec-policy-isakmp-1-10]q
6.在接口上应用安全策略
[R1]int s0/2/0
[R1-Serial0/2/0]ipsec policy 1 //在接口上应用安全策略
7、最后在出口指缺省路由
[R1]ip route-static
R3:
[R3]ip route-static
[R3]acl number 3000
[R3-acl-adv-3000]rule permit ip source
[R3]ike proposal 10
[R3-ike-proposal-10]encryption-algorithm 3des-cbc
[R3-ike-proposal-10]authentication-method pre-share
[R3-ike-proposal-10]authentication-algorithm md5
[R3-ike-proposal-10]dh group2
[R3-ike-proposal-10]sa duration 86400
[R3-ike-proposal-10]q
[R3]ike peer R1
[R3-ike-peer-r1]exchange-mode main
[R3-ike-peer-r1]pre-shared-key h
[R3-ike-peer-r1]local-
[R3-ike-peer-r1]remote-address
[R3-ike-peer-r1]remote-name R1
[R3-ike-peer-r1]q
[R3]ipsec proposal r3
[R3-ipsec-proposal-r3]transform esp
[R3-ipsec-proposal-r3]esp encryption-algorithm 3des
[R3-ipsec-proposal-r3]esp authentication-algorithm md5
[R3-ipsec-proposal-r3]encapsulation-mode tunnel
[R3-ipsec-proposal-r3]q
[R3]ipsec policy 1 10 isakmp
[R3-ipsec-policy-isakmp-1-10]security acl 3000
[R3-ipsec-policy-isakmp-1-10]proposal r3
[R3-ipsec-policy-isakmp-1-10]ike-peer R1
[R1-ipsec-policy-isakmp-1-10]pfs dh-group2
[R3-ipsec-policy-isakmp-1-10]sa duration time-based 86400
[R3-ipsec-policy-isakmp-1-10]q
[R3]int s0/2/0
[R3-Serial0/2/0]ipsec policy 1
[R3-Serial0/2/0]q
四、测试结果
[R1]ping -
五、调试命令:
1.显示IKE对等体配置参数
[R1]dis ike peer
---------------------------
IKE Peer: r3
exchange mode: main on phase 1
pre-shared-key cipher nw1kqzgZJnA=
peer id type: ip
peer ip address:
local ip address:
peer name: R3
nat traversal: disable
dpd:
---------------------------
[R1]
2.显示当前ISAKMP SA的信息
[R1]dis ike sa
total phase-1 SAs: 1
connection-id peer flag phase doi
----------------------------------------------------------
3
2
flag meaning
RD--
[R1]
3.显示每个IKE提议的配置参数
[R1]dis ike sa
total phase-1 SAs: 1
connection-id peer flag phase doi
----------------------------------------------------------
3
2
flag meaning
RD--
[R1]dis ike proposal
priority authentication authentication encryption Diffie-Hellman duration
method algorithm algorithm group (seconds)
---------------------------------------------------------------------------
10 PRE_SHARED MD5 3DES_CBC MODP_1024 86400
default PRE_SHARED SHA DES_CBC MODP_768 86400
[R1]
4.显示IPsec安全策略信息
[R1]dis ipsec policy
===========================================
IPsec Policy Group: "1"
Using interface: {Ethernet0/1/0}
===========================================
-----------------------------
IPsec policy name: "1"
sequence number: 10
mode: isakmp
-----------------------------
security data flow : 3000
selector mode: standard
ike-peer name: r3
perfect forward secrecy: DH group 2
proposal name: r1
IPsec sa local duration(time based): 86400 seconds
IPsec sa local duration(traffic based): 1843200 kilobytes
[R1]
5.显示IPSEC安全提议信息
[R1]dis ipsec proposal
IPsec proposal name: r1
encapsulation mode: tunnel
transform: esp-new
ESP protocol: authentication md5-hmac-96, encryption 3des
[R1]
6.显示IPSEC SA的信息
[R1]dis ipsec sa
===============================
Interface: Ethernet0/1/0
path MTU: 1500
===============================
-----------------------------
IPsec policy name: "1"
sequence number: 10
mode: isakmp
-----------------------------
connection id: 3
encapsulation mode: tunnel
perfect forward secrecy: DH group 2
tunnel:
local address:
remote address:
Flow :
sour addr:
dest addr:
ersal: N
[outbound ESP SAs]
spi: 1974141924 (0x75ab03e4)
proposal: ESP-ENCRYPT-3DES ESP-AUTH-MD5
sa remaining key duration (bytes/sec): 1887435624/84789
max sent sequence-number: 15
udp encapsulation used for nat traversal: N
[R1]
7.显示IPSEC处理的报文信息
[R1]dis ipsec statistics
the security packet statistics:
input/output security packets: 14/14
input/output security bytes: 1176/1176
input/output dropped security packets: 0/1
dropped security packet detail:
not enough memory: 0
can't find SA: 1
queue is full: 0
authentication has failed: 0
wrong length: 0
replay packet: 0
packet too long: 0
wrong SA: 0
[R1]
上一篇: redmine3的安装和升级
下一篇: centos7 安装 ipython3
- H3C基本命令大全
52801
- H3C IRF原理及 配置
39788
- Python exit()函数
34171
- python全系列官方中文文档
29924
- python 获取网卡实时流量
24815
- 1.常用turtle功能函数
24642
- python 获取Linux和Windows硬件信息
23030
- 天天基金网数据接口
16414
- Selenium使用代理IP&无头模式访问网站
14666
- Selenium&Pytesseract模拟登录+验证码识别
14175
- LangGraph Studio可视化
434°
- LangSmith开发-应用入门
417°
- LangGraph开发-多轮对话问答机器人
491°
- LangGraph开发-条件分支/循环图实战
489°
- LangGraph开发-生态介绍,入门demo实战
529°
- LangChain-接入12306-HTTP MCP智能体
661°
- LangChain接入自定义爬虫-MCP工具
625°
- LangChain接入Filesystem-MCP工具
657°
- LangChain搭建MCP服务端和客户端流程
739°
- LangGraph与MCP技术概述
665°
- 姓名:Run
- 职业:谜
- 邮箱:383697894@qq.com
- 定位:上海 · 松江